Key takeaways
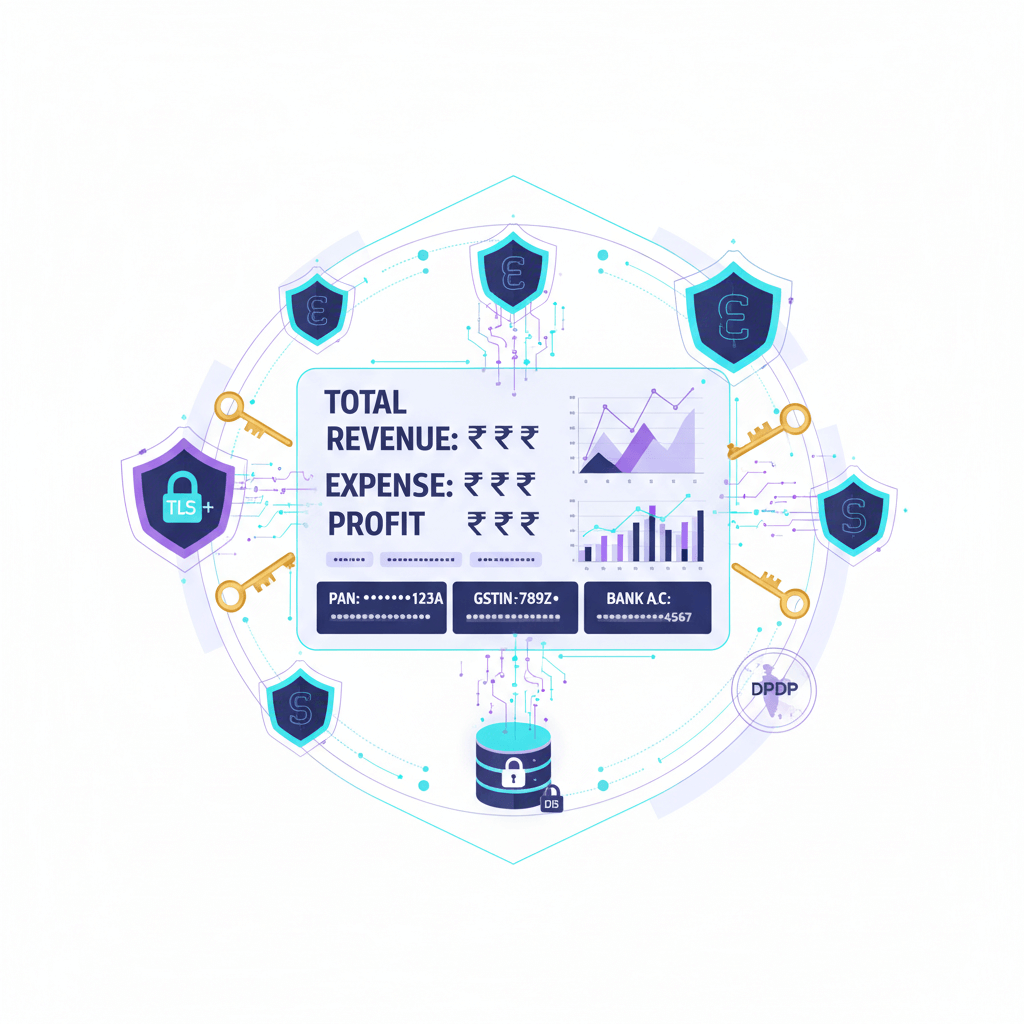
- Data encryption turns readable financial data into coded text that only a valid key can unlock, protecting PAN, GSTIN, invoices, payroll, and bank info end to end.
- Use TLS 1.2 or 1.3 for data in transit and AES‑256 for data at rest across databases, disks, and backups, plus role based access and MFA for control.
- Strong key management with KMS or HSM, rotation, and recovery plans is as critical as the encryption itself.
- Virtual accounting works best when files, chats, and approvals stay inside a secure portal, not email or consumer chat apps.
- Encryption supports DPDP Act expectations in India, reduces breach risk, and builds audit ready trails for GST, TDS, and MIS workflows.
- AI Accountant’s CA led model, central dashboard, and secure repository reduce risky sharing and keep documents and filings visible in one place.
What is data encryption for accounting services
Encryption uses math to scramble data so that only a holder of the right key can read it. A widely used standard, AES‑256, protects financial records at rest, while TLS 1.2 or 1.3 protects them in transit. Banks, ERPs, and accounting portals rely on these standards today. See primers and best practices at Lucid and PK Tech.
Three places encryption applies:
- In transit: Protects browser to app, API calls, and secure file transfer with TLS. Avoid plain email for tax files, use secure links instead. Sources: Integ, Infinity Globus.
- At rest: Covers disks, databases, cloud buckets, and backups with AES‑256, optionally field level encryption for PAN or bank numbers. References: Lucid, Integ, Infinity Globus.
- In use: Emerging methods let systems compute on encrypted data with minimal exposure, useful to watch for future needs. Reference: Lucid.
Encryption differs from two related tools: hashing converts passwords into one way fixed strings you cannot reverse, and tokenization replaces sensitive values with stand ins so the originals stay hidden. Accounting teams use encryption when they must later read the real data for reconciliations and filings. Background: Lucid and AI Accountant.
Why data encryption matters in accounting
Accounting data is a prime target: IDs like PAN and GSTIN, payroll, e‑invoices, and vendor records draw attackers. Risks include phishing, man in the middle snoops on open wifi, and lost laptops without disk encryption. See Integ and DiamondIT.
Shadow IT—sharing tax PDFs via email or chat, or putting bank exports in personal drives—creates accidental leaks and audit slowdowns.
Regulatory and client expectations add weight. India’s DPDP Act emphasises safeguarding personal data, boards ask for evidence, and clients expect NDAs, retention control, and breach response. Encryption, logged access, and end to end protection help you comply and maintain trust. References: AI Accountant, Infinity Globus, Integ, Lucid.
The encryption stack explained for accountants
You do not need deep tech skills to verify protections—ask for simple proofs.
Transit controls
Require TLS 1.2+ on every app and API, enable HSTS, validate certificates, and use secure file transfer for bulk data. Reference: Integ.
At rest controls
Use AES‑256 on databases, disks, and backups. Add field level encryption for high sensitivity fields like bank accounts or Aadhaar to limit blast radius. Sources: Lucid, Infinity Globus, PK Tech.
Key management
Keep encryption keys in a KMS or HSM, rotate regularly, segregate keys from data, log every access, and plan recovery paths, because without keys, backups are useless. Sources: Integ, Lucid.
Backups and archives
Encrypt every backup, escrow critical keys, and test restores often. If a restore fails, the backup never counted. References: Integ, Infinity Globus.
Endpoints and mobiles
Enable full disk encryption on laptops (e.g., BitLocker), enforce device policies and remote wipe to prevent data loss on theft. See Integ.
Credentials and secrets
Hash passwords, use a secrets manager for API keys, and enforce MFA everywhere to reduce impact from credential compromises. See Practice Protect.
Integrations
For bank feeds and payment gateways, require TLS, store API keys in a vault, rotate keys, and scope permissions minimally. Reference: Accounting Seed.
Where data encryption for accounting services fits in daily workflows
Bank statements and reconciliations
Uploads and feeds should be over TLS, and stored files encrypted at rest, including exports and downloaded reports. Source: Integ.
Payment gateway reconciliations
Gateway to ledger APIs must use TLS, with keys stored in a secure vault and rotated. Reference: Infinity Globus.
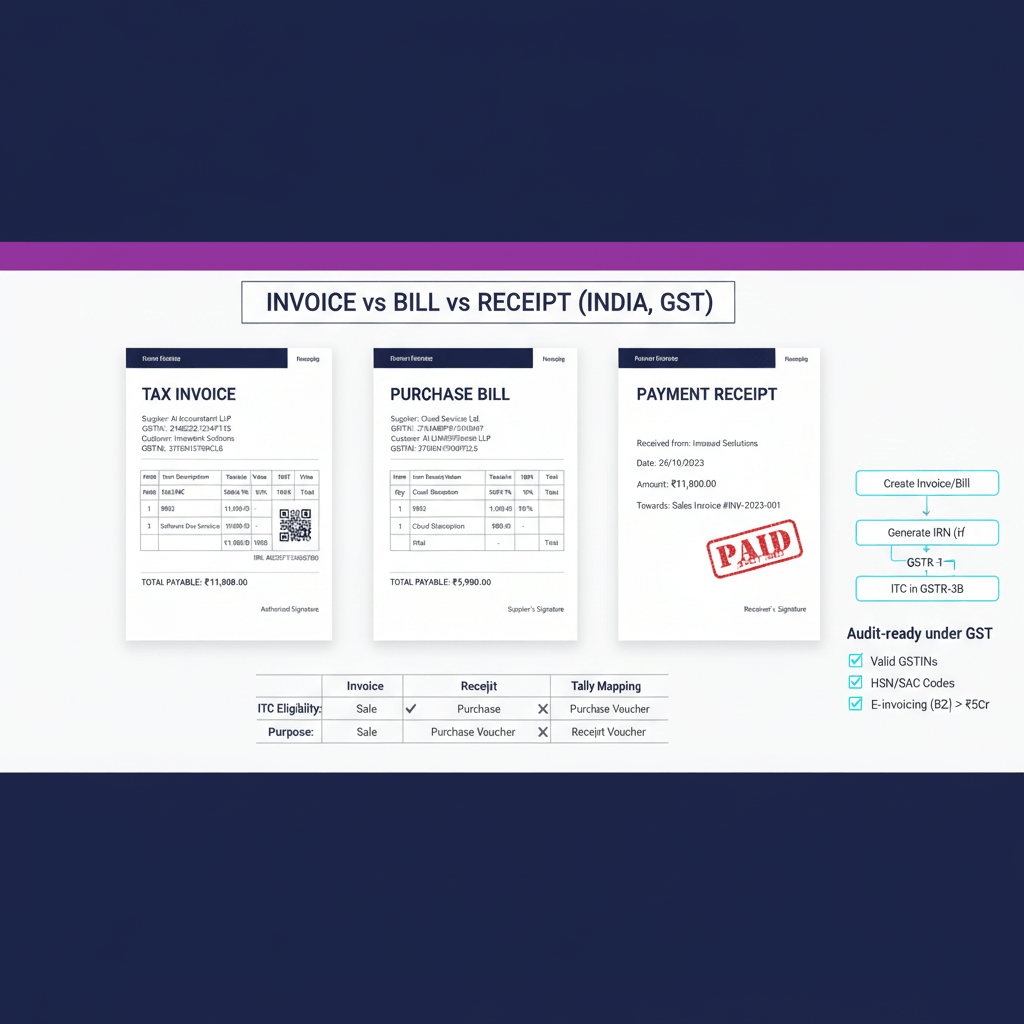
GST and TDS filings
GSTR‑1, 3B, 9, 9C and TDS forms 26Q, 24Q, 27Q, 26QB/26QC/26QD contain high sensitivity data; store challans, returns, and workpapers in an encrypted repository with role based permissions. See Integ.
Document repository and CA communication
A central portal with encrypted storage and in app discussions reduces email and chat risks, and preserves clean audit trails. Sources: Infinity Globus, Practice Protect.
E invoicing and vendor exchange
Use end to end encryption and expiring secure links for invoice exchange. Avoid emailing PDFs with tax IDs. Reference: Infinity Globus.
MIS dashboards
Dashboards should enforce HTTPS and encrypt summaries at rest. Source: Accounting Seed.
Auditor sharing
Share via expiring secure links with access logs, not email attachments. See Integ.
How to evaluate a provider’s encryption posture
- Transit and at rest coverage: TLS 1.2+ everywhere and AES‑256 on all stores and backups. References: Integ, Lucid.
- Key management: KMS or HSM in place, rotation, access logs, and clear recovery process. Sources: Integ, Lucid.
- Access controls: RBAC and MFA enforced, with periodic access reviews. Reference: Practice Protect.
- Document handling: Secure repository in use, email and chat discouraged for file exchange. Source: Infinity Globus.
- Monitoring and response: Audit logging, alerting, and a clear breach notification plan. See Integ.
- Policies: Data retention, deletion, and residency documented and auditable. Reference: Infinity Globus.
- Third parties: Due diligence on bank feed providers and sub processors for encryption and access control. Source: Integ.
- Proof: Whitepapers, security overviews, and ISO 27001 or SOC 2 type reports for assurance. References: Infinity Globus, PK Tech.
Implementation roadmap for internal standards
- Map and classify data flows: Trace sources to destinations and tag risks, prioritising PAN, bank accounts, payroll. Reference: Integ.
- Enforce transit and at rest encryption: TLS everywhere, AES‑256 for databases, file stores, and backups, verify cloud defaults. Sources: Lucid, PK Tech.
- Tokenize where you can: Use tokens for flows that do not need real values, keep token vaults isolated, encrypt sensitive fields, and centralise sharing in a portal. Reference: Lucid.
- Lock down access with RBAC and MFA: Grant least privilege, enforce MFA, and review access quarterly. Source: Practice Protect.
- Manage keys and train people: KMS or HSM with rotation and recovery, plus short training on phishing and safe handling. References: Integ, Lucid.
- Test and monitor: Test backup restores, scan for open shares, track logs, and fix gaps quickly. Reference: Integ.
How AI Accountant virtual accounting supports secure handling of financial data
AI Accountant is a CA led managed service for bookkeeping, GST, TDS, and income tax. The central dashboard shows live books, filings, and documents, reducing risky email or chat sharing and keeping a clean audit trail. This helps protect PAN and GSTIN during preparation and filing, while giving you a clear view of what is due and what is filed. Learn about secure document flows in our guide on document management for accounting.
System first collaboration means files live in an encrypted repository, secure links replace attachments, and internal notes stay in one place—simple steps that lower exposure without slowing work.
Practical tips for clients to boost protection
- Use strong sign in controls: Turn on MFA, use long passwords and a manager, and offboard promptly. Reference: Practice Protect.
- Use portals for file exchange: Upload bank files and tax docs through the portal, not email. Read why in our note on paperless accounting systems. Supporting view: Integ.
- Avoid shared credentials: Give each user a separate account and use scoped API keys. See Practice Protect.
- Protect devices and networks: Turn on full disk encryption, keep systems updated, avoid public wifi for filings, and use a hotspot if needed. Source: Integ.
Secure accounting tools and portals that support encryption
If you are reviewing your stack, prioritise portals with TLS 1.2+, AES‑256 at rest, MFA, RBAC, secure file sharing, audit logs, and clear retention controls. Ask how keys and backups are handled. See guidance at Integ, Lucid, and Practice Protect.
Shortlist: AI Accountant, QuickBooks Online, Xero, Zoho Books, FreshBooks, Sage Intacct.
Mini case vignette on encryption in practice
Before
A freelancer shared GST workpapers via WhatsApp and email. Files carried tax IDs and bank info, were easy to forward, and impossible to track.
After
They moved to an encrypted repository with expiring links. The audit ran ~40% faster because evidence lived in one place with a clean log, and exposure risk dropped. Background: Infinity Globus.
Glossary of simple terms
- Encryption in transit: TLS protects data moving between devices and servers. Source: Integ.
- Encryption at rest: AES‑256 protects stored data in disks, databases, and backups. Source: Integ.
- Key management: Creating, storing, rotating, and guarding keys with KMS or HSM. Source: Integ.
- Tokenization: Replacing sensitive values with tokens, so the real values stay hidden. Reference: Lucid.
- Hashing: One way transforms for passwords, not reversible. Reference: Practice Protect.
- MFA: Multi factor authentication, a second step to sign in. Reference: Practice Protect.
- RBAC: Role based access control, giving users only what they need. Reference: Practice Protect.
Putting it all together for your team
Encryption is a trust choice as much as a tech choice. It keeps PAN, GSTIN, payroll, and bank data safe, supports DPDP duties, and enables faster, audit friendly workflows. In virtual accounting, pairing encryption with a central dashboard and repository changes the game.
If you want a simple start this week:
- Ask vendors to confirm TLS 1.2+ in transit and AES‑256 at rest, including backups.
- Move all file sharing into a secure portal with MFA and expiring links.
- Turn on full disk encryption on every laptop and verify restore tests for backups.
Need help mapping flows for GST and TDS and setting guard rails. AI Accountant can walk you through a short review and show how the dashboard and repository keep data in one secure lane without slowing your books.
Book a demo or security chat, explore Virtual Accounting, see GST and TDS, and review dashboard features.
FAQ
Is TLS alone sufficient for securing our accounting data across GST, TDS, and MIS workflows
No. TLS protects data in motion only. You also need AES‑256 encryption at rest for databases, file stores, and backups to cover the full lifecycle, plus RBAC and MFA for access. Sources: Integ, Lucid.
Which systems should definitely run AES‑256 at rest in a CA managed or virtual accounting stack
All primary ledgers, document repositories, bank export storage, GST and TDS workpapers, payroll files, reporting data marts, and all backups. Field level encryption is recommended for PAN, bank accounts, and Aadhaar. References: Lucid, Infinity Globus, PK Tech.
How should a startup founder verify a provider’s key management without deep technical audits
Ask for a written overview showing KMS or HSM use, rotation frequency, separation of keys from data, access logging, and tested recovery. Request evidence from a recent restore test. AI Accountant can provide a security review on request.
What is the practical difference between encryption, hashing, and tokenization for accounting data
Encryption is reversible with keys, used for ledgers and filings you must read. Hashing is one way, ideal for passwords. Tokenization swaps sensitive values with stand ins, reducing exposure in payment or vendor flows. See Lucid.
Will encryption slow monthly closes or MIS dashboards for finance heads
Modern databases and clouds encrypt with minimal overhead. For field level encryption, cache summaries and encrypt only the sensitive columns. Most teams see negligible performance impact with proper design.
How do we securely share large working folders with auditors without email friction
Use an encrypted repository with expiring, permission scoped links and full access logs. Avoid attachments. AI Accountant supports secure file exchange inside the dashboard, keeping an audit trail by default.
What does the DPDP Act expect from finance teams regarding encryption and data handling
Protect personal data in transit and at rest, restrict access via roles, retain only as needed, and be ready to demonstrate controls. Encryption plus RBAC, MFA, and retention rules aligns well with these duties. Reference: Lucid.
How should CAs and controllers manage API secrets for bank feeds and payment gateways
Store API keys in a secrets manager, never in code or spreadsheets, rotate regularly, scope least privilege, and enforce TLS for all calls. Reference: Accounting Seed.
What checks should a finance head include in a quarterly encryption and access review
Confirm TLS coverage, AES‑256 on all stores and backups, key rotation logs, MFA and RBAC status, backup restore tests, expiring link policies, and an access diff for joins, moves, and exits.
How does an AI enabled service like AI Accountant reduce everyday leak risks versus email and chat
By keeping files in an encrypted repository, using secure links with expiry, consolidating chats and approvals in app, and enforcing RBAC and MFA. This removes shadow IT patterns and builds a single audit trail.
Do we need field level encryption, or is full disk and database encryption enough
Disk and database encryption cover broad risks, but field level encryption for PAN, bank accounts, or Aadhaar reduces blast radius in partial exposures and limits who can view the raw values. It is a pragmatic extra layer for high sensitivity data.
What immediate steps can a bootstrapped startup take to uplift encryption without a big budget
Enable TLS 1.2+ everywhere, turn on built in at rest encryption in your cloud and databases, enforce MFA, shift file exchange into a secure portal, and test a backup restore. These changes are mostly configuration, not custom builds.