Key takeaways
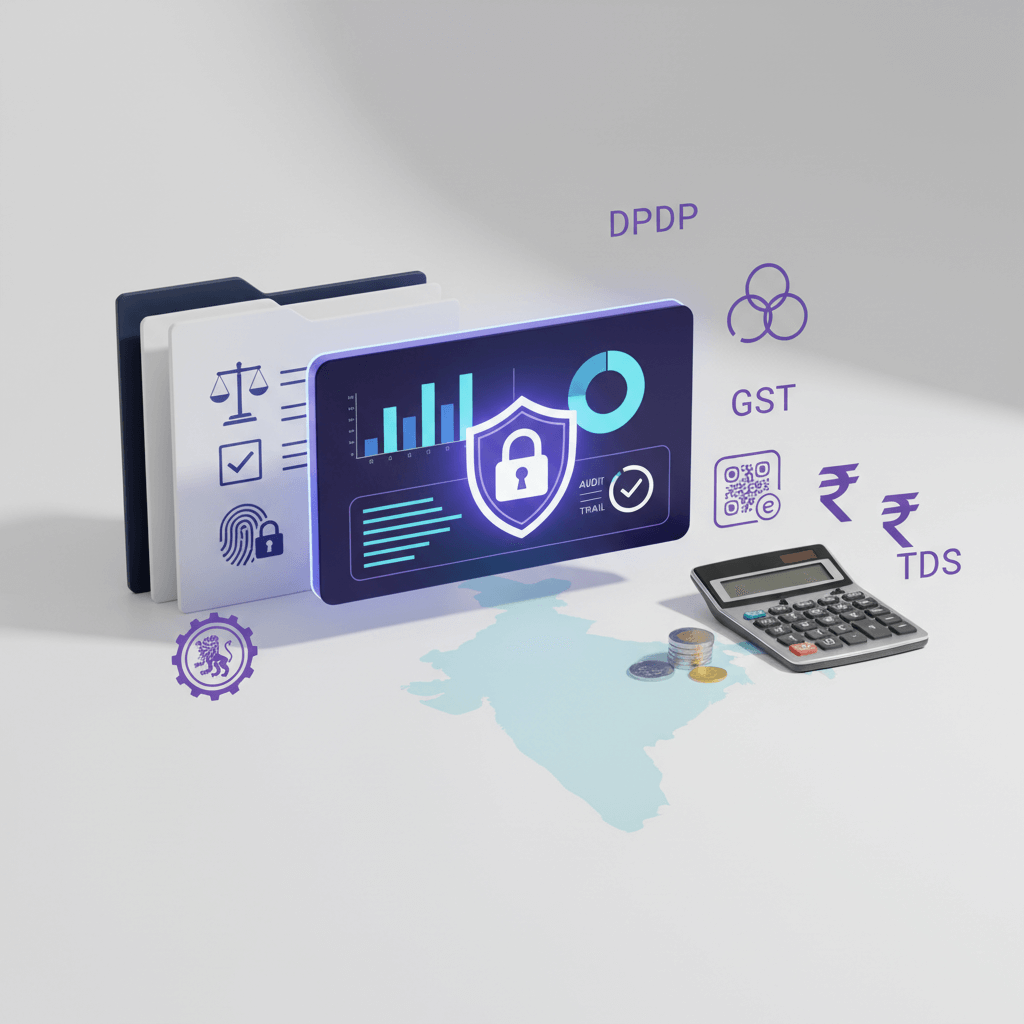
- Financial data compliance in India means aligning daily accounting workflows with the DPDP Act (Rules now in force, full enforcement by May 2027), IT Act, RBI frameworks, GST and Income Tax retention rules, MCA record keeping, and CERT‑In log directions, so you can prove audit readiness fast.
- Payroll, GST filings, TDS records, vendor KYC, bank reconciliations, and ledgers all qualify as personal data under DPDP; protect them with access control, encryption, immutable logs, and a retention matrix tied to each law.
- Data mapping is now auditable under the DPDP Rules 2025. Businesses that complete their data inventory early reduce last minute scrambles and penalty exposure (fines can reach ₹250 crore).
- A practical roadmap, centralize documents, enable MFA, standardize maker‑checker reconciliations, and map proofs to every filing, cuts audit prep time from weeks to days.
- Track five KPIs monthly: on time filing rate, reconciliation completion, access review status, MFA coverage, and vendor DPA coverage to demonstrate control to auditors and boards.
- A CA‑led virtual accounting service embeds these controls into bookkeeping and filings by default, replacing scattered spreadsheets with a managed, audit‑ready system without hiring a full in‑house team.
Financial Data Security Compliance: What's New in 2026
Until November 2025, the DPDP Act existed as a framework without enforceable rules. That changed on November 13, 2025, when the DPDP Rules 2025 were notified, triggering a phased compliance timeline. Full Data Fiduciary obligations become enforceable by May 13, 2027, which makes 2026 the critical preparation window.
The operational shift is significant. Data mapping is no longer a best practice; it is auditable. Every business handling personal financial data (payroll PII, vendor PAN details, employee salary slips) must now inventory data flows, purposes, and retention periods. The Data Protection Board of India (DPBI) is operational and can enforce breach reporting, consent management, and security safeguard obligations. Breach notification to the DPBI is now a contractual and legal requirement, not just a policy aspiration.
Who does this hit hardest? Businesses processing high volume personal data, think CA firms managing payroll for dozens of clients, startups storing vendor KYC at scale, or SMEs with employee counts above 50, face the steepest compliance curve. An EY survey in 2026 found that 70% of professionals remain unfamiliar with the Rules, even as financial services firms lead readiness efforts.
The cost of inaction is concrete: penalties up to ₹250 crore for inadequate safeguards, blocked vendor onboarding from enterprise clients who demand DPDP proof, and audit findings that flag missing data maps or unsigned Data Processing Agreements.
What to do right now:
- Complete your personal data inventory by Q2 2026, covering payroll, GST proofs, TDS records, and vendor KYC.
- Update all Data Processor contracts with DPDP security and breach notification clauses before Q3 2026.
- Run a gap assessment against the Rules and document remediation steps.
Teams using a CA‑managed virtual accounting service can phase in these safeguards alongside monthly bookkeeping cycles rather than treating compliance as a separate project.
Introduction to Compliance for Financial Data Security
Compliance for financial data security means following the law and using strong controls so financial data remains confidential, correct, and available. Think payroll, GST filings, TDS records, vendor KYC, bank reconciliations, and ledgers. These demand protected storage, proper access, and clear logs that show who did what and when.
Why this matters now in India is clear. The DPDP Act allows very large fines for weak safeguards. Breaches can attract penalties up to two hundred and fifty crore rupees. Beyond fines, a data leak or failed audit damages trust with clients, blocks new deals, and can disrupt operations.
GST and Income Tax audits expect strong records and proof of control. This is not just a tech job. It is an operations job that blends accounting discipline with security discipline.
Practical compliance is a daily workflow, not a one time policy. Controls must live inside bookkeeping, reconciliations, filings, and reviews.
This India first guide draws on the DPDP Act and Rules 2025, the IT Act and Rules on reasonable security, RBI cyber and fraud guidance, MCA and GST rules, and CERT‑In directions about logs stored in India. If you serve overseas clients, add a light view of GDPR or CCPA basics such as consent and data minimization.
Sources: DLA Piper, India Data Protection, eQomply, DPDP Act Compliance Guide
Regulatory Landscape in India for Compliance for Financial Data Security
DPDP Act 2023 and Rules 2025
Use reasonable security safeguards for personal data, including payroll and vendor KYC. The Rules now detail specific requirements: technical and organisational measures proportional to risk, breach notification to the DPBI, and Data Principal rights covering access, correction, and erasure (2026 update).
Apply encryption, access control, and logging. If you are a Significant Data Fiduciary (SDF), you must conduct Data Protection Impact Assessments, appoint a Data Protection Officer, and schedule independent audits. Data mapping is now the mandatory first step and is auditable under the Rules (2026 update).
The phased enforcement timeline eases integration with existing RBI and SEBI frameworks. Initial notice and consent operations plus security upgrades are expected through 2026, with all Data Fiduciary obligations enforceable by May 13, 2027.
Sources: Fisher Phillips, India's New Data Privacy Rules, ANDE Global, DPDP Rules Compliance Checklist
IT Act and Rules on Reasonable Security Practices
Protect data with standard measures: process checks, technical controls, and audit logs for key financial transactions. The DPDP Rules now add a personal data lens on top. Payroll PII, vendor PAN data, and employee financial records must satisfy both the IT Act's reasonable security standard and DPDP's safeguard requirements.
RBI Cybersecurity and Fraud Frameworks
Regulated entities need board approved cyber policies, live monitoring, and fast incident reporting. Even if you are not a bank, borrow these good practices. Digital lending rules push for data localisation in payments, and the RBI Fraud Risk Management direction expects strong audit trails.
DPDP incident playbooks now align with RBI fraud monitoring expectations, creating a single response workflow for both regulatory streams.
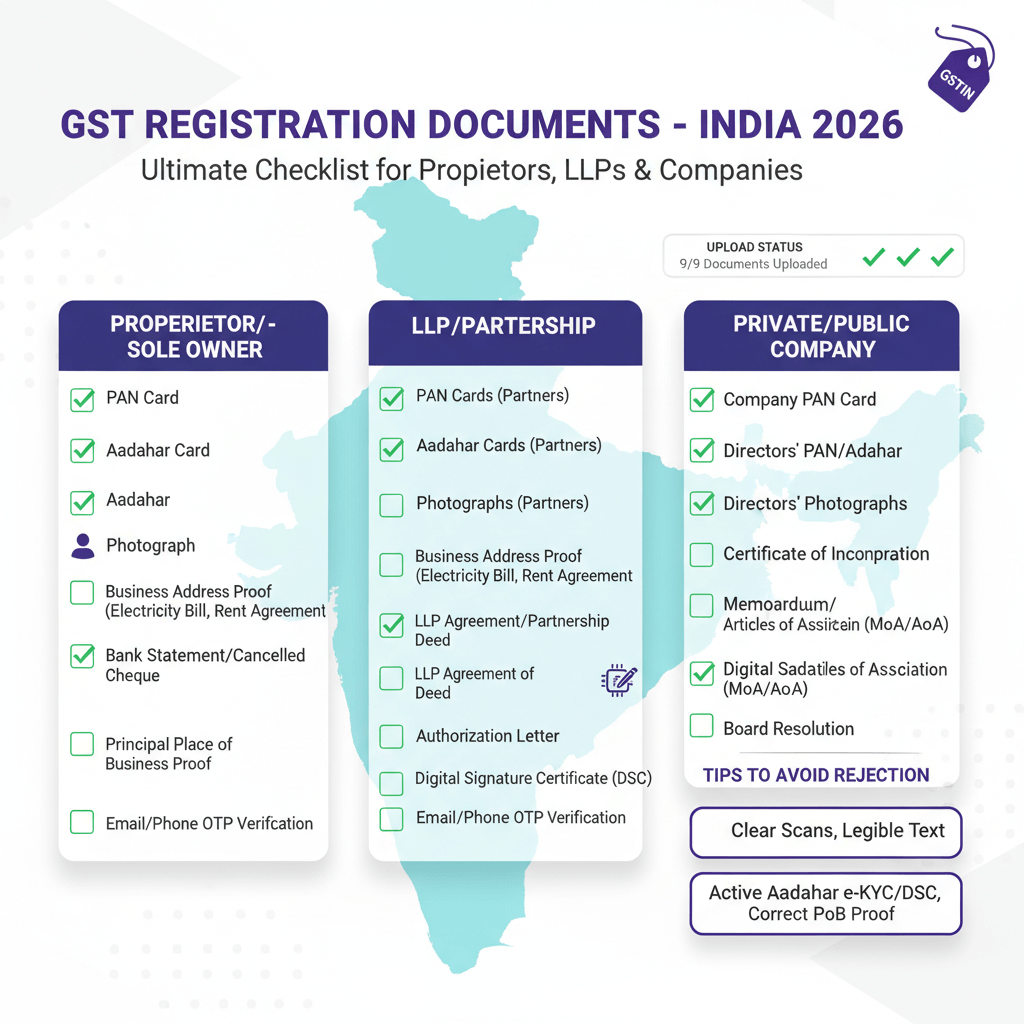
GST, Income Tax, Companies Act Retention and Reporting
Retain GST invoices generally for seventy two months from the due date of the annual return for the year. Income Tax records often run six years or more if assessments are pending. Maintain MCA registers and minutes safely as required. TDS reporting needs complete proofs such as challans and returns like Form 24Q and Form 26Q.
Under DPDP, tie retention periods to erasure obligations. Once the retention period for a record type expires and no legal hold applies, delete the personal data (2026 update).
Source: GST Portal, Government of India
CERT‑In Directions 2022
Keep logs for financial transactions and store them in India for set periods to support detection and response. These logs now also support DPDP breach response workflows.
Payments and PCI DSS
If you handle card data, implement PCI DSS controls. RBI also asks certain payment data to be stored in India. If you only reconcile card settlements but do not store cardholder data, your PCI scope may be limited. Confirm with your payment provider.
Use this map as a working checklist. Ask your CA‑led virtual accounting partner how they meet these items through process design, secure storage, and audit trails.
Global Data Compliance Touchpoints for Cross Border Work
Data minimization
Only collect and store what you need. If a field is not required for a filing or business purpose, do not store it. This principle applies equally under DPDP, GDPR, and CCPA.
Consent and transparency
Explain how you use data and obtain clear consent when required. DPDP is consent heavy compared to GDPR, which allows additional legal bases. Factor this difference into your workflows if you serve EU clients.
Larger clients may ask for ISO 27001 or SOC 2 certification. Even without certification, adopt core habits: access reviews, encryption, change control, and continuous monitoring. Vendor contracts now require DPDP clauses covering security, breach notice, and deletion (2026 update).
Source: Bass Berry, India's Data Privacy Rules for Business
Core Pillars of Compliance for Financial Data Security
Data Mapping and Gap Assessment
This is now a Phase 1 priority under the DPDP Rules. Inventory all financial PII flows: who collects it, what is collected, where it is stored, which vendors process it, and how long it is retained. Expand your existing RBI and IT Act asset lists to include DPDP scope. This step is auditable (2026 update).
Governance and Risk Assessment
Create a data inventory. Map flows, owners, and access. If you are a Significant Data Fiduciary, conduct a DPIA for high risk finance processes (payroll at scale, vendor KYC). Review risks quarterly and track fixes. Schedule annual independent audits if you are an SDF.
Access Control and Least Privilege
Grant only needed access. Enable multi factor authentication on all finance and document tools. Review access quarterly. Keep logs and alert on unusual access patterns. Role based access with maker‑checker for reconciliations and ledger entries is the baseline expectation.
Secure Data Handling
Classify data as public, internal, confidential, or restricted. Use protected sharing for PII and financial records. Block unapproved sharing channels such as personal email or public links.
Encryption and Masking
Encrypt data in transit and at rest. This covers payroll slips, TDS working papers, and vendor KYC files. Mask sensitive fields in reports when full values are not required.
Logging and Audit Trails
Keep event logs for access, changes, and key actions. Maintain immutable audit trails for bank reconciliations, ledger edits, and filings. Retain these per CERT‑In and DPDP requirements.
Vendor Management and Contracts
Run due diligence on every data processor. Sign Data Processing Agreements that cover security, breach notice timelines, and deletion or return of data. Under the DPDP Rules, vendor DPAs must include specific security clauses (2026 update). Maintain a current vendor list and review it quarterly.
Business Continuity and Backups
Back up accounting data and documents. Test recovery often. Keep an offsite or cloud copy in India where data localisation applies.
Incident Response
Write a simple playbook. Define who to alert, how to contain, and how to report to the Data Protection Board of India if required. The DPBI is now operational and expects fiduciaries to notify breaches per the Rules (2026 update). Test the playbook yearly.
Retention and Deletion
Create a retention matrix. For example, keep GST records at least seventy two months, Income Tax records around six years or more. After retention expires and no legal hold applies, implement auto erasure of personal data per DPDP obligations.
Training and Continuous Monitoring
Train staff and vendors on e‑invoice handling, TDS data care, and DPDP basics. An EY survey found 70% of professionals remain unfamiliar with the DPDP Rules, so role specific training matters. Run internal audits and vulnerability checks. Fix issues fast. Repeat training every six months.
Map Compliance for Financial Data Security to Daily Accounting Work
Bookkeeping and Ledgers
Use maker‑checker for entries and edits. Post monthly close sign off notes. Keep an immutable audit trail for all journal changes and ledger entry modifications. Run integrity checks for outliers.
Reconciliations
Separate duties. One person prepares, another reviews and closes. This segregation is central to proving financial data security compliance during audits.
Keep evidence and exception logs. Clear exceptions within thirty days. Target one hundred percent reconciliation completion every month.
GST Filings
Control e‑invoice processes. Maintain reverse charge mechanism documentation. Map HSN codes and rates. Keep proofs for GSTR‑1 and GSTR‑3B filings with working papers and acknowledgments tagged to each return number.
TDS and Income Tax
Validate PAN data before filing. Track challans and BSR codes. Keep proofs for returns like 24Q and 26Q. Track Form 16 issuance and delivery. These proofs are your first line of defence when answering the question: how to prove we can recover data for an audit?
Payroll
Handle personal data with DPDP grade care. Payroll records contain employee PII and qualify as personal data under the Act. Restrict access. Encrypt payslips at rest and in transit. Log every access event to payroll records.
ROC and MCA
Keep statutory registers and minutes in a secure repository with version history and controlled access. Treat these as confidential documents.
Documents and Communication
Use a central document store with version control and access logs. Avoid scattering data across email, chat apps, or personal drives. A secure dashboard with your CA team reduces leak risk and speeds audits.
How Virtual Accounting Supports Compliance for Financial Data Security
CA led processes
Monthly bookkeeping, reconciliations, and year end closes run with maker‑checker workflows. Each step creates an audit ready trail. The CA team coordinates with statutory auditors so evidence is complete and organised.
Secure dashboard
View revenue, expenses, cash, burn, and runway. Track GST, TDS, Income Tax, and MCA calendars. Monitor filing status. Store documents in a structured repository with controlled access and retained logs.
AI insights flag trends and possible issues early. This supports DPDP compliant access controls, MFA enforcement, and encryption at rest and in transit.
DPDP readiness built in
A CA‑led virtual model can scope DPIA requirements, track vendor DPA coverage, and maintain the evidence library needed for the phased DPDP timeline through May 2027.
Impact
You reduce penalties and lower breach risk. You align with DPDP and RBI style expectations without hiring a full in house team. You replace scattered spreadsheets and emails with a managed system that is audit ready by default.
Implementation Roadmap for Startups, SMEs, and Freelancers
This roadmap is phased to align with the DPDP Rules enforcement timeline through May 2027.
- Q2 2026: Baseline data map, list your data. Map flows for payroll, GST, TDS, and sales. Note personal data fields. Do a gap assessment against the DPDP Rules, the IT Act, RBI frameworks, and client expectations. Plan a DPIA if you are a Significant Data Fiduciary. This step is now auditable.
- Centralize, pick one system for books, documents, and compliance calendars. A virtual accounting dashboard helps consolidate everything into a single controlled environment.
- Define roles and MFA, set roles, approvals, and maker‑checker. Enable MFA across all finance tools. Target one hundred percent MFA coverage.
- Configure calendars and alerts, set due dates for GSTR‑1, GSTR‑3B, TDS, advance tax, ITR, and ROC forms. Add reminders and escalation paths.
- Standardize templates and retention, create templates for invoices, e‑invoice data, RCM memos, TDS working papers, and reconciliation packs. Build a retention matrix tied to GST (seventy two months), Income Tax (six years or more), and DPDP erasure obligations.
- Run monthly reconciliations, close bank and gateway reconciliations each month. Age and track exceptions. Target closure within thirty days.
- Q3 2026: Write incident and vendor procedures, define breach response with a DPBI notification path. Update vendor contracts with DPDP security and breach clauses. Maintain a current vendor list and signed DPAs.
- Train teams, run short training on DPDP basics, e‑invoice controls, TDS accuracy, and secure sharing. Repeat every six months. Address the 70% awareness gap.
- Q4 2026: Hold quarterly reviews with your CA, check access logs, reconciliation status, filing on time rates, and exceptions. Agree on next actions.
- Q1 2027: Test and audit, if you are an SDF, complete your DPIA and run a full simulation. Test the incident playbook. Review all evidence packs.
- May 2027: Full compliance, notice, consent, and breach operations live. Use dashboard feedback and AI alerts to refine controls. Adjust roles and thresholds as you scale.
Practical Checklist for Compliance for Financial Data Security
- Complete a personal data inventory covering all financial PII flows
- Enable MFA on all finance and document tools with one hundred percent coverage
- Maintain a single secure repository with access control and version history
- Stop uncontrolled shares and public links
- Keep monthly reconciliation evidence and sign offs
- Map filing proofs to each return number and payment
- Use a retention matrix that covers GST, Income Tax, ROC, and DPDP erasure
- Maintain a vendor list and signed DPAs with DPDP security clauses
- Test your incident playbook once a year, including DPBI notification steps
- Run quarterly access reviews and fix gaps
- Keep an active compliance calendar with alerts and owners
- Conduct breach response drills and document outcomes
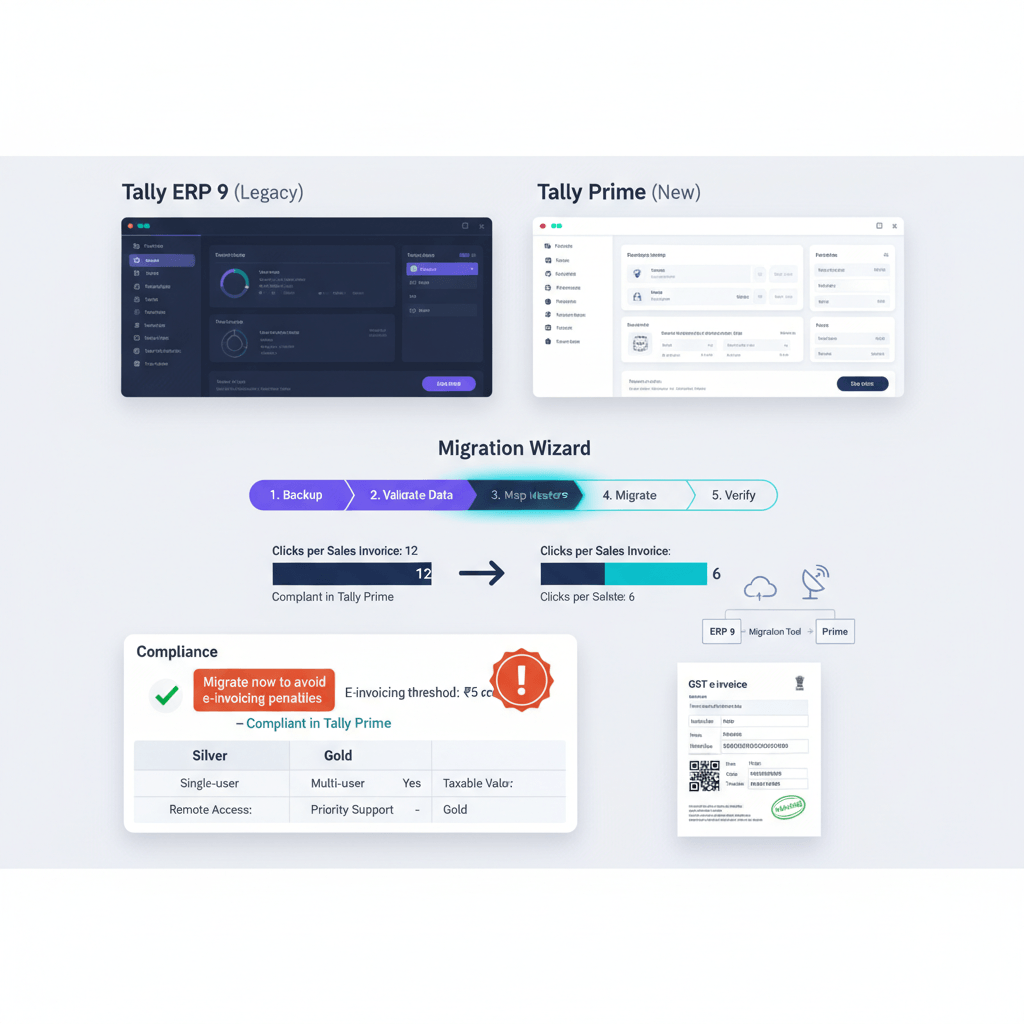
Recommended Accounting Tools that Support Data Security and Compliance
- AI Accountant, a CA‑led virtual accounting service with a secure dashboard for books, GST, TDS, Income Tax, payroll, and ROC support. Includes a document repository, compliance calendar, AI insights, maker‑checker workflows, and controlled access with DPDP aligned logging, visit AI Accountant.
- QuickBooks Online, cloud accounting with user roles, audit logs, and bank feeds.
- Xero, cloud ledgers with advanced reconciliation and user permissions.
- Zoho Books, India friendly GST features, role based access, and workflows.
- Tally Prime, popular in India with strong inventory and GST support when paired with secure backup and access policies.
- FreshBooks, simple invoicing and expense tracking for freelancers and small teams.
- Sage Intacct, mid market financial management with strong controls and reporting.
No tool is perfect. How you set access, structure approvals, and keep evidence matters most.
KPIs and Evidence to Prove Compliance for Financial Data Security
- On time filing rate, target one hundred percent for GST, TDS, Income Tax, and ROC. Keep dashboard logs and acknowledgments.
- Reconciliation completion, target one hundred percent monthly. Maintain exception logs and close items within thirty days.
- Access reviews, target zero overdue reviews each quarter. Keep a signed review note and change list.
- MFA enablement, target one hundred percent of users on all finance and storage tools. Keep screenshots or system reports.
- Audit query turnaround, target closure under seven days. Track dates and outcomes.
- Retention compliance, target one hundred percent records tagged with the right hold time and DPDP erasure schedule. Keep a retention matrix and samples.
- Breach drill completion, target at least one tested incident response simulation per year. Document findings and improvements.
- Vendor DPA coverage, target one hundred percent of data processors under signed DPDP compliant agreements. Track in a vendor register.
Common Pitfalls and How to Avoid Them in Compliance for Financial Data Security
- No data mapping, start today. Under the DPDP Rules 2025, data maps are auditable and non negotiable. Inventory personal data flows for payroll, GST, TDS, and vendor KYC before anything else.
- Scattered data in email or chat, move to a central dashboard and repository with access control. Scattered data makes it nearly impossible to prove you can recover records for an audit.
- No maker‑checker for entries and filings, add approvals and role based steps for key actions. One person should never initiate and approve the same transaction.
- Ignoring DPDP in payroll, classify payroll as personal data. Encrypt storage and sharing. Restrict access. Keep logs of every access event.
- Weak RCM or HSN documentation, maintain memos and working papers that show decisions and rates. Missing documentation creates exposure during GST audits.
- Delayed reconciliations, use automated reminders and a monthly close calendar. Review exceptions weekly. Data compliance in financial services depends on timely, evidenced reconciliation.
- Outdated vendor contracts, update Data Processing Agreements with DPDP security and breach notification clauses now. Do not wait for the May 2027 deadline.
Closing Thoughts on Compliance for Financial Data Security
Compliance for financial data security is a daily habit inside bookkeeping, reconciliations, GST and TDS filings, payroll, and ROC work. When you add access control, logs, encryption, and clear retention, you protect your business and save time in every audit.
The DPDP Rules 2025 have shifted this from theoretical to operational. Data mapping is auditable. Breach notification is enforceable. Vendor contracts need updating. The May 2027 full enforcement date means 2026 is your preparation window. Early movers build trust with clients and auditors while avoiding penalties that can reach ₹250 crore.
You do not need a large in house team to reach this level. A CA‑led virtual accounting service brings structure, visibility, and control through one dashboard and a dedicated team. Start with three steps: map your personal data, centralize tools, and turn on MFA. Then add maker‑checker, monthly reconciliations, and vendor DPAs. With that base, the rest becomes much easier.
FAQ
What is the DPDP Rules 2025 compliance timeline for financial data
The DPDP Rules were notified on November 13, 2025, and full Data Fiduciary obligations become enforceable by May 13, 2027 (2026 update). Businesses should complete data mapping and gap assessments by Q2 2026, update vendor contracts by Q3 2026, and have all notice, consent, and breach operations live before the May 2027 deadline.
What is the difference between security and compliance for finance teams in India
Security covers technical safeguards like encryption, access control, logging, and monitoring. Compliance means meeting specific laws such as the DPDP Act, IT Act, and GST rules, and proving adherence with policies, evidence, and audits. A CA‑led virtual accounting model ties these together by embedding controls in bookkeeping and filings while maintaining audit ready proof.
How to prove we can recover data for an audit
Maintain a central, version controlled document repository with access logs and monthly reconciliation evidence packs. Map every filing proof to its return number, challan, and payment reference. Test your backup and recovery process at least once a year and document the results. Auditors look for a clear chain from source document to filed return.
Which records must I retain, and for how long, to stay compliant during GST and Income Tax audits
Keep GST invoices for at least seventy two months from the due date of the annual return for the year. Income Tax records usually need six years or more if assessments are pending. MCA registers and minutes must be maintained per Companies Act requirements. After retention periods expire and no legal hold applies, delete personal data per DPDP erasure obligations (2026 update).
Do freelancers and sole proprietors really need DPDP grade controls for client data
Yes, if you handle personal or financial data you fall under the DPDP Act and the IT Act. Keep it simple: centralize documents in a secure portal, enable MFA, restrict sharing to controlled channels, and maintain clear access logs. These steps satisfy reasonable security expectations without heavy setup.
When do I need a Data Protection Impact Assessment under DPDP
A DPIA is required if you are designated a Significant Data Fiduciary or you process high risk personal data at scale, such as payroll for many clients or vendor KYC across multiple entities. Scope it to cover access, encryption, logging, and retention for finance processes, and record the mitigations you implement (2026 update).
What does data compliance in financial services require for vendor management
Sign Data Processing Agreements with every vendor that handles personal financial data. Each DPA must cover security safeguards, breach notification timelines, data deletion or return, and DPDP specific clauses (2026 update). Maintain a current vendor register, run due diligence before onboarding, and review DPA compliance quarterly.
-01%201.svg)